Top news for this month: Water is wet, cats are fluffy, cows yield milk, and LastPass got hacked. What is surprising about this, at least to me, is that people continue to be surprised when it turns out that giving something as sensitive as every password you have to another company for safekeeping isn’t the best idea in the world.
This isn’t new
LastPass breaches are a gift that keeps on giving. If you’re not aware of how often this happens, let’s go back down memory lane:
- On 03 May 2011, LastPass staff discovered some “anomalies” (read: a breach) in their servers that they did not describe in much detail. Still, it was enough to convince them to tell customers (in a security notice that is now a very elegant little 404 page) that they should reset their master passwords. Apparently, the hackers may have copied the server salt and several salted passwords. I’m piecing together what I can but information on this breach is scant nowadays.
- Only four years later, on June 2015, LastPass posted yet another product update (which is also now a 404 page) indicating that unknown malicious actors took a good chunk of per-user salts.
- In 2016, security expert Mathias Karlsson posted a lengthy and excellent piece of research that demonstrated he could exploit the LastPass browser extension to collect plaintext passwords from malicious websites. Although this particular post referred to LastPass, I feel the need to emphasize that the details found within outline the flaws of using any browser extension tied to a password management service, self-managed or not.
- In 2017 and 2019, well-known security expert Tavis Ormandy added to Mathias Karlsson’s work demonstrating even more extensive security flaws in the browser extension.
- In 2022, a long-term breach occurred where a hacker stole the customer database and several customer vaults. Without going into too much detail, this became the most significant breach that LastPass suffered until the one we currently are discussing. The stolen information includes backend source code, customer billing addresses, partial credit card numbers, and several other things I doubt you’d want some stranger who has deep grease marks on their keyboard to have.
This isn’t even an exhaustive list; it’s just what I managed to put together after about 20 minutes of light googling.
Let’s be fair to LastPass, though… I’m not writing this to demonize their company. After all, it would be completely dishonest to single them out when a range of different password managers have had similar issues.
For example, there’s the Norton LifeLock breach that allowed hackers to collect a large trove of customer passwords. And then there’s the Passwordstate breach where hackers pushed a fake update that downloaded DLLs into customer computers and allowed them to grab an unknown number of passwords.
The point I’m trying to make is that if you think that breaches are a phenomenon unique to LastPass, you’re sorely mistaken.
Let’s learn a few lessons here
I’d like to walk you through my thought process when it comes to password management:
- Your passwords grant access to various services that are very important to your daily life
- Therefore, your passwords are like the keys to your house
- When you leave your house, you often keep your keys in your person
- Keeping your passwords and the keys and hashes associated with them in a remote location is akin to giving the keys to your house to someone else every time you leave
Can you trust that person? Are you sure? Have you been good friends for several years?
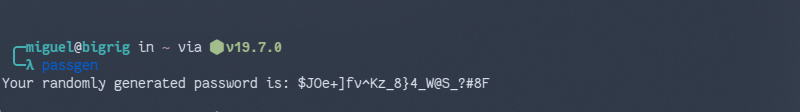
Hopefully, you can see what I’m getting at here without me having to explain it exhaustively. But in case you didn’t quite get the point, it’s important to practice password hygiene independently and find a way to manage your passwords in a way that you personally can control. This involves a solution that provides a similar level of security to what many password managers promise (and actually achieve it!) while also ensuring a certain level of convenience.
I’ll probably elaborate on this a bit later in an update.
What do you use?
I’ve found Buttercup to be very satisfying. It works on every major platform (except, unfortunately, FreeBSD), it has a strong level of organization, and it can sync an encrypted vault via popular cloud services like Google Drive. The vault will be encrypted with a salt that you generate, allowing you full control of your passwords.
If you don’t feel comfortable putting the vault on a cloud service, it will also sync via WebDAV to any server you have.
Do you have any other suggestions for independent password management? Let’s talk about it!
